TRUST CLAUDIU POPA’S 35 YEARS OF CERTIFIED EXPERTISE IN TECHNOLOGY & SECURITY
CANADA’S CYBERSAFETY EXPERT
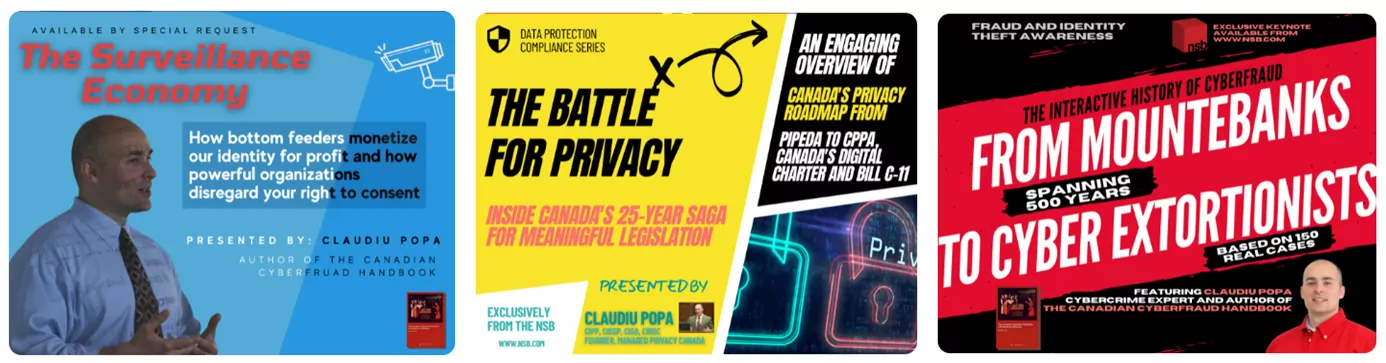
Need a public speaker for corporate and community audiences? Let Claudiu engage, entertain & educate with an impactful, interactive keynote and illustrated research data.
as featured on
SPEAKER REEL LAUNCH
Now Available: Claudiu’s Official Speaker Reel
Planning a professional event? Make it impactful with an engaging cybersecurity keynote. Click here to to request Claudiu’s Speaker Pack including headshots, professional bio and media kit.
EXCLUSIVE
Check Out Claudiu’s 2024 Cyber Talks Calendar!
Claudiu Popa is Canada’s subject matter expert on everything cyber, from data protection to digital literacy, cybercrime to identity fraud, crypto, artificial intelligence and the latest emerging tech. Enjoy a vast array of professional talks and custom keynotes year round.


new Media Kit
Now Available: Claudiu’s 2024 Speaking Kit!
Speaking agencies and editorial professionals qualify for the free 8-page media kit. Get yours now.
TOP-RATED CYBERSECURITY EXPERT
Why Invite Claudiu Popa to Keynote Your Event?
ABOUT CLAUDIU POPA
Claudiu’s Story
Claudiu Popa specializes in security strategy and information asset protection and advocates for education and risk assessment for all businesses. Popa co-founded Canada’s only cybersafety foundation, where he oversees academic research and data-driven education programs. Over the past two decades, he has designed processes, testing methods, and standardized security auditing and information assurance systems that scale across supply chains.


Contact Us
Book Your AMA Today
Claudiu Popa specializes in security strategy and information asset protection and advocates for education and risk assessment for all businesses. Popa co-founded Canada’s only cybersafety foundation, where he oversees academic research and data-driven education programs. Over the past two decades, he has designed processes, testing methods, and standardized security auditing and information assurance systems that scale across supply chains.
Professional Activities
Guaranteed Audience Engagement
Public Speaking
Claudiu Popa specializes in delivering keynote presentations, participating in panel discussions and conducting professional workshops.
Media Commentary
Claudiu Popa wields his expertise to explain complex concepts in cybersecurity and protection to your viewers and listeners.
Article Writing
Claudiu Popa literally wrote the book on digital literacy and continues to ruminate on current cybersecurity trends in his blog, Bad Privacy.
Captivating Presentations
New talks and seminars are added quarterly to Claudiu’s growing catalogue of interactive workshops, custom keynotes and professional courses.

Original Publications
Claudiu has authored important publications on privacy rights, cybersecurity and cyberfraud, backed by years of research and media commentary.





